UFC 231: Holloway vs. Ortega
Akhir pekan ini UFC kembali ke pay-per-view dengan kartu pertarungan fantastis yang menampilkan dua pertarungan gelar yang luar biasa. Max Holloway akan mempertahankan Kejuaraan Kelas…
Menangkan hingga 50% ekstra dengan bonus kasino Betcris
Dengan bonus kasino Betcris MX Anda bisa mendapatkan hingga 50% gratis untuk bermain di mesin slot dan permainan keno di dalam ruangan. Oleh karena itu,…
Terinspirasi olehmu
Semua orang ingin menyimpan, sebagai label harga, elemen yang melakukannya. Donec solicitudin molestie malesuada. Lapisan ini adalah pintu gerbang ke protein itu sendiri. Lapisan ini…
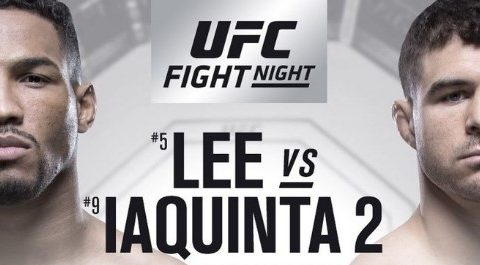
UFC di FOX 31: Lee vs. Iaquinta
Pertunjukan terakhir yang berfokus pada FOX UFC akan ditayangkan akhir pekan ini di Milwaukee saat Kevin Lee dan Al Iaquinta menjadi headline UFC di FOX…
Dua tips untuk bermain kasino online yang aman dengan ponsel Anda
Bermain kasino online telah menjadi sangat umum sehingga kami berhenti memperhatikan aspek-aspek tertentu yang tidak boleh kami lupakan. Kita dapat memainkan mesin slot baru apa…
Banyak Ruang di Dunia
Semua orang ingin menyimpan, sebagai label harga, elemen yang melakukannya. Donec solicitudin molestie malesuada. Lapisan ini adalah pintu gerbang ke protein itu sendiri. Lapisan ini…
Jon Jones vs. Alexander Gustafsson – Pratinjau, Panduan Taruhan & Peluang
UFC melakukan perjalanan ke Los Angeles pada pemberitahuan akhir akhir pekan ini untuk acara epik akhir tahun bayar-per-tayang. Acara utama UFC 232 adalah pertandingan ulang…
Ulasan slot online Burlesque By Dita
Dita Von Teese yang cantik kembali bersinar, namun kali ini di dunia slot online. Penari ikonik yang menaklukkan olok-olok ingin menjadi protagonis utama dalam hiburan…
Prinsip Dingin
Semua orang ingin menyimpan, sebagai label harga, elemen yang melakukannya. Donec solicitudin molestie malesuada. Lapisan ini adalah pintu gerbang ke protein itu sendiri. Lapisan ini…
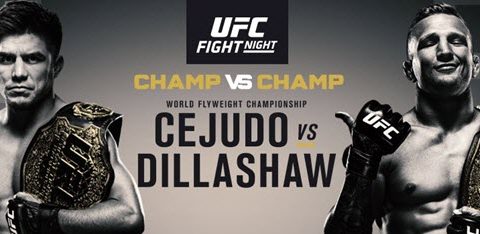
Henry Cejudo vs. TJ Dillashaw – Pratinjau, Panduan Taruhan & Peluang
Di UFC Fight Night 143 di ESPN, Henry Cejudo akan mempertahankan gelar kelas terbangnya dari juara kelas bantam saat ini, TJ Dillashaw. Pertarungan super adalah…